Measured against security baselines
Validate your Windows environment against industry-standard security benchmarks (like CIS) and best practices to reduce attack surface and harden your infrastructure.
What Windows Security Benchmark Review covers
Identify insecure configurations and systematically harden your Windows ecosystem.
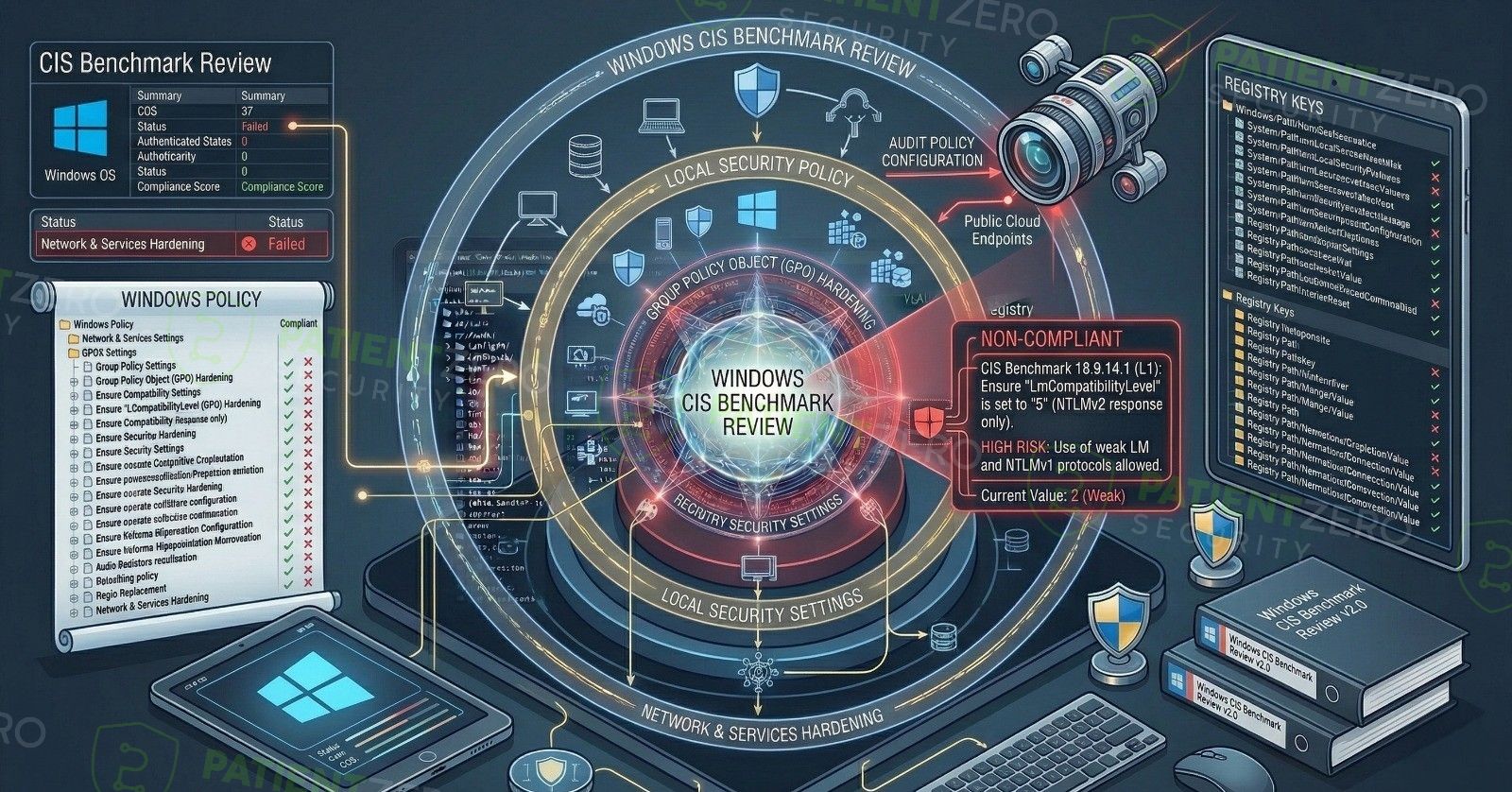
A Windows Security Benchmark Review evaluates your Windows infrastructure—including servers, workstations, and Active Directory environments—against recognized industry standards such as CIS (Center for Internet Security) Benchmarks. This structured review helps your organization establish a defense-in-depth posture inside the network.
The assessment focuses on identifying misconfigurations, weak policies, missing security updates, and excessive privileges that could be leveraged by an attacker. We thoroughly review Group Policy Objects (GPOs), patch management processes, user rights assignments, and local system policies across your environments.
Our team provides actionable recommendations to harden your systems without disrupting critical business operations. Validating configurations actively ensures your Windows environment is fortified and resilient against both internal and external threats, rather than relying on default settings.
Our security benchmark process
A systematic approach from understanding your environment to actionable remediation guidance.
What you take away
Clear, actionable intelligence to improve your internal security posture.
Ready to act on your benchmark findings?
Schedule a consultation to walk through the compliance report, prioritize fixes, and strengthen your infrastructure securely.

