When client-side trust becomes risk.
Thick Client Penetration Testing evaluates the security of desktop applications that communicate with backend services, APIs, or databases.
What Thick Client Penetration Testing covers
Comprehensive analysis of client-side controls and backend interactions.
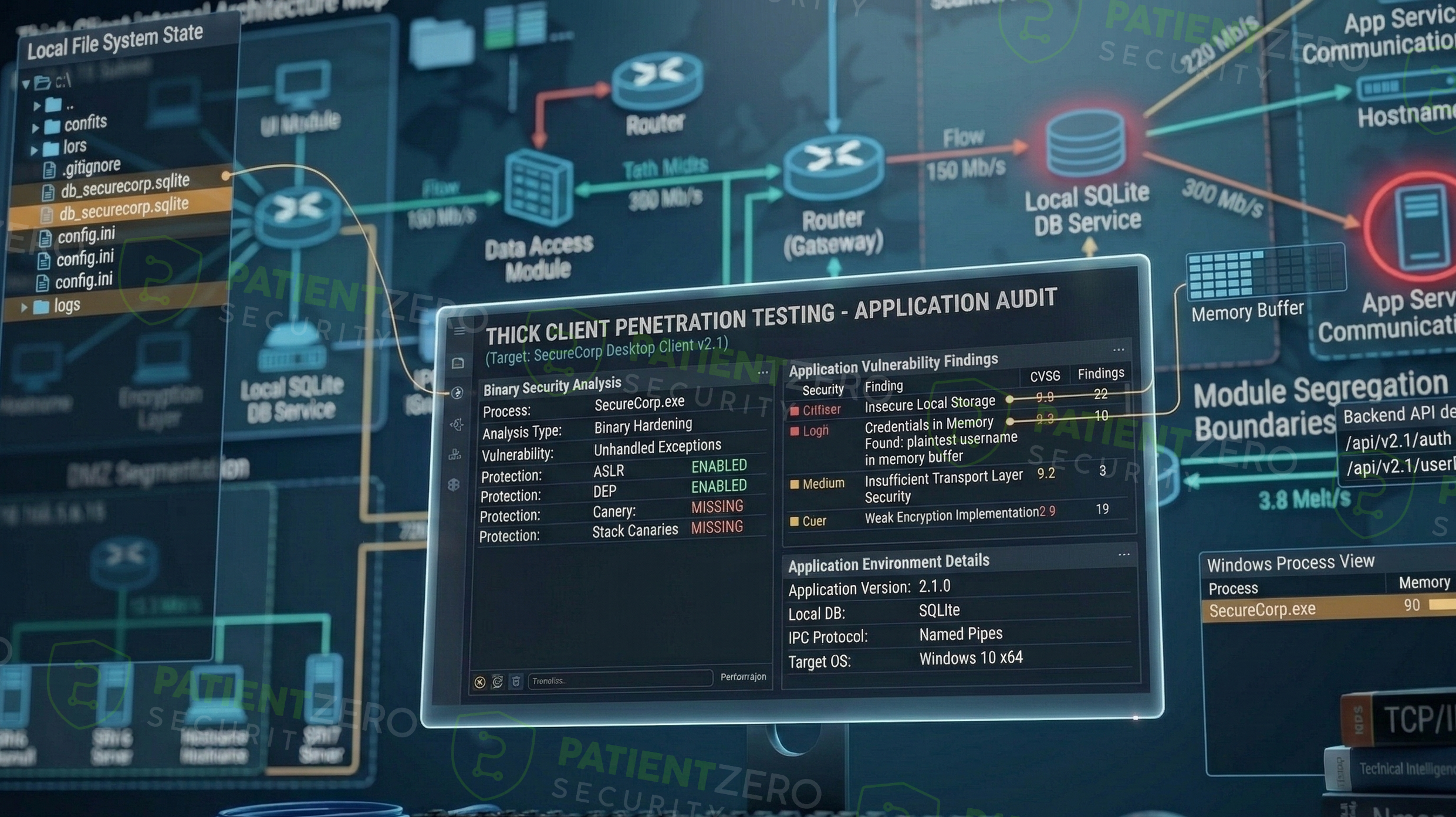
Thick Client Penetration Testing evaluates the security of desktop applications that communicate with backend services, APIs, or databases, where critical logic and trust decisions are often enforced on the client side. The service focuses on identifying whether client-side controls can be bypassed or manipulated to gain unauthorized access to backend systems or sensitive data.
Testing follows a manual, attacker-driven approach aligned with PTES and NIST SP 800-115, combining binary analysis, traffic inspection, and request manipulation. Tools such as x64dbg, dnSpy, Wireshark, and Burp Suite are used alongside manual techniques to analyze application logic, intercept client-server communication, and validate whether backend authorization is properly enforced independent of the client.
The assessment primarily reports individual client-side and client–server vulnerabilities, while also evaluating whether these issues can be chained to achieve higher-impact outcomes such as backend compromise or unauthorized data access. All findings are validated through controlled exploitation to support effective remediation prioritization.
Our thick client penetration testing process
From binary analysis to backend exploitation.
What you take away
Actionable results for engineering and development teams.
Ready to secure your applications?
Every engagement includes a formal report and optional live readout call.

