Security, line by line
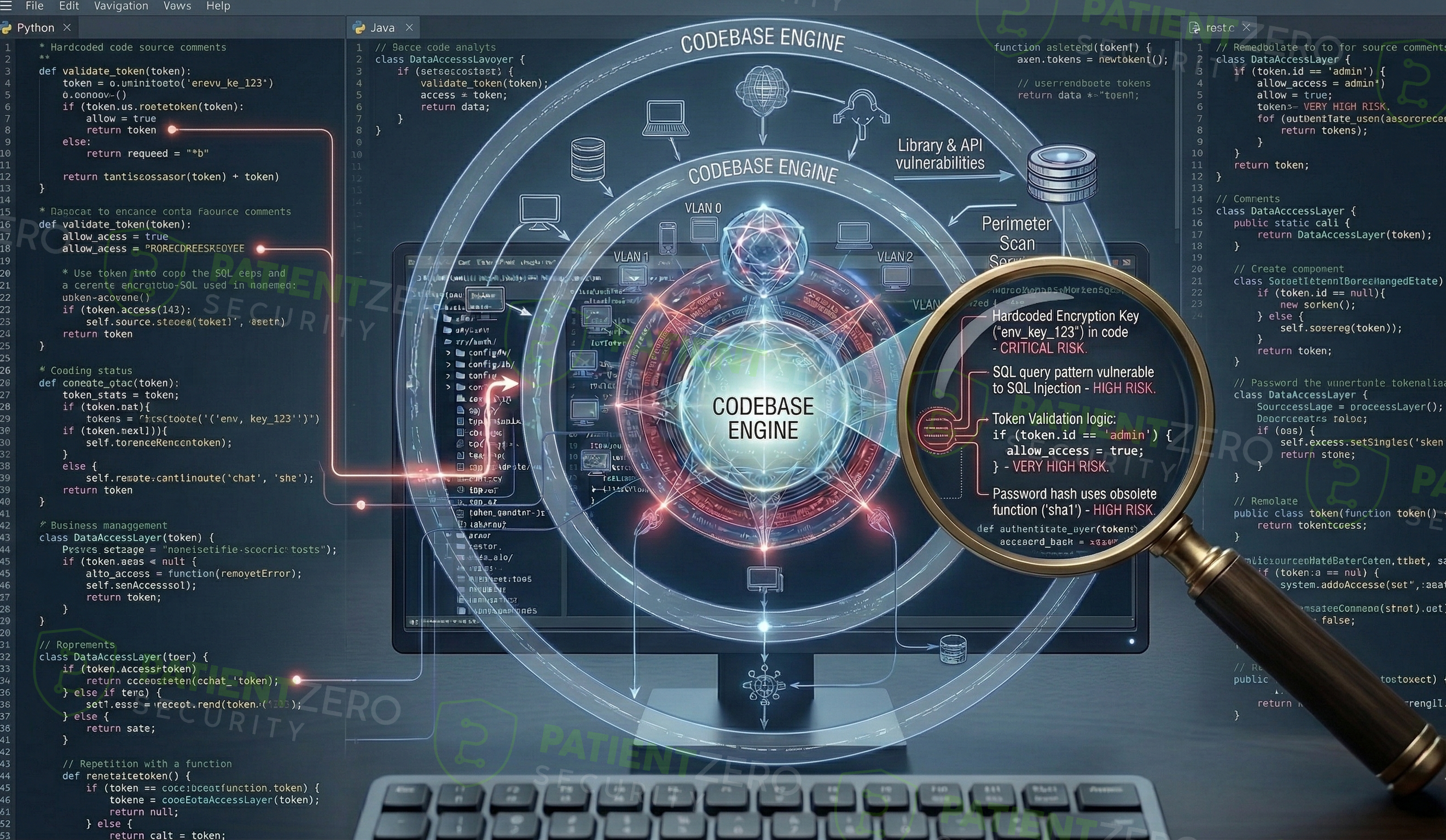
Secure Code Review evaluates application source code to identify security weaknesses in authentication, authorization, input validation, cryptography, and sensitive business logic.
What Source Code Review covers
Detect vulnerabilities early in the development lifecycle.
Secure Code Review evaluates application source code to identify security weaknesses in authentication, authorization, input validation, cryptography, and sensitive business logic. The review helps organizations detect vulnerabilities early in the development lifecycle, reducing the risk of exploitation in production environments.
The assessment follows OWASP Secure Coding Practices to evaluate how securely code is written and structured, while leveraging OWASP Top 10, OWASP ASVS, and CWE Top 25 for coverage and risk classification. The review combines automated static analysis to identify common insecure patterns with manual code review to uncover logic flaws, insecure design decisions, and implementation weaknesses that automated tools alone cannot detect.
Where applicable, and when a supporting test environment is provided, identified issues may be validated through controlled exploitation to demonstrate real-world impact, following a white-box testing approach without performing a full penetration test.
Our source code review process
A systematic approach from understanding the codebase to actionable remediation guidance.
What you take away
Clear, actionable intelligence to improve your application security posture.
Ready to act on your code review findings?
Schedule a consultation to walk through the report, prioritize fixes, and plan secure coding improvements.

