Visibility before exploitation.
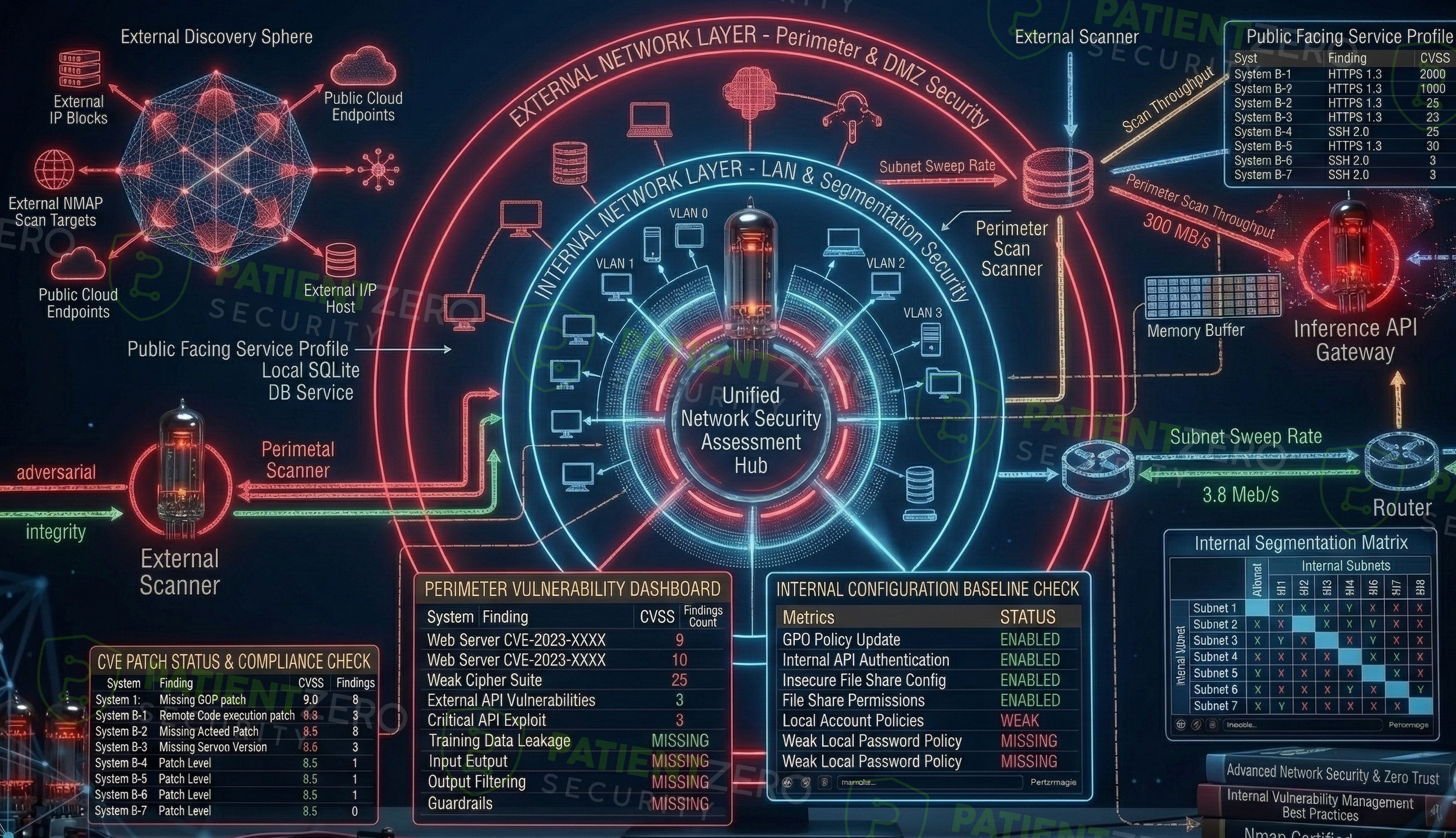
Network Security Assessments provide visibility into vulnerabilities and misconfigurations across network-connected systems using authenticated and unauthenticated scanning techniques.
What Network Security Assessment covers
Comprehensive visibility into your network security posture.
Network Security Assessments provide visibility into vulnerabilities and misconfigurations across network-connected systems using authenticated and unauthenticated scanning techniques. This service is designed to identify exposed services, outdated software, insecure configurations, and missing patches across the network environment.
The assessment primarily uses Nessus to perform structured vulnerability scanning across defined IP ranges and network segments. The goal is to provide organizations with a clear understanding of their network security posture and to highlight areas requiring remediation before they are exploited.
Our network assessment process
A systematic approach to identifying and validating risks.
What you take away
Clear, actionable intelligence to improve your security posture.
Ready to act on your network security findings?
Schedule a consultation to walk through the results and plan remediation across your environment.

