Your Network perimeter, from outside and within
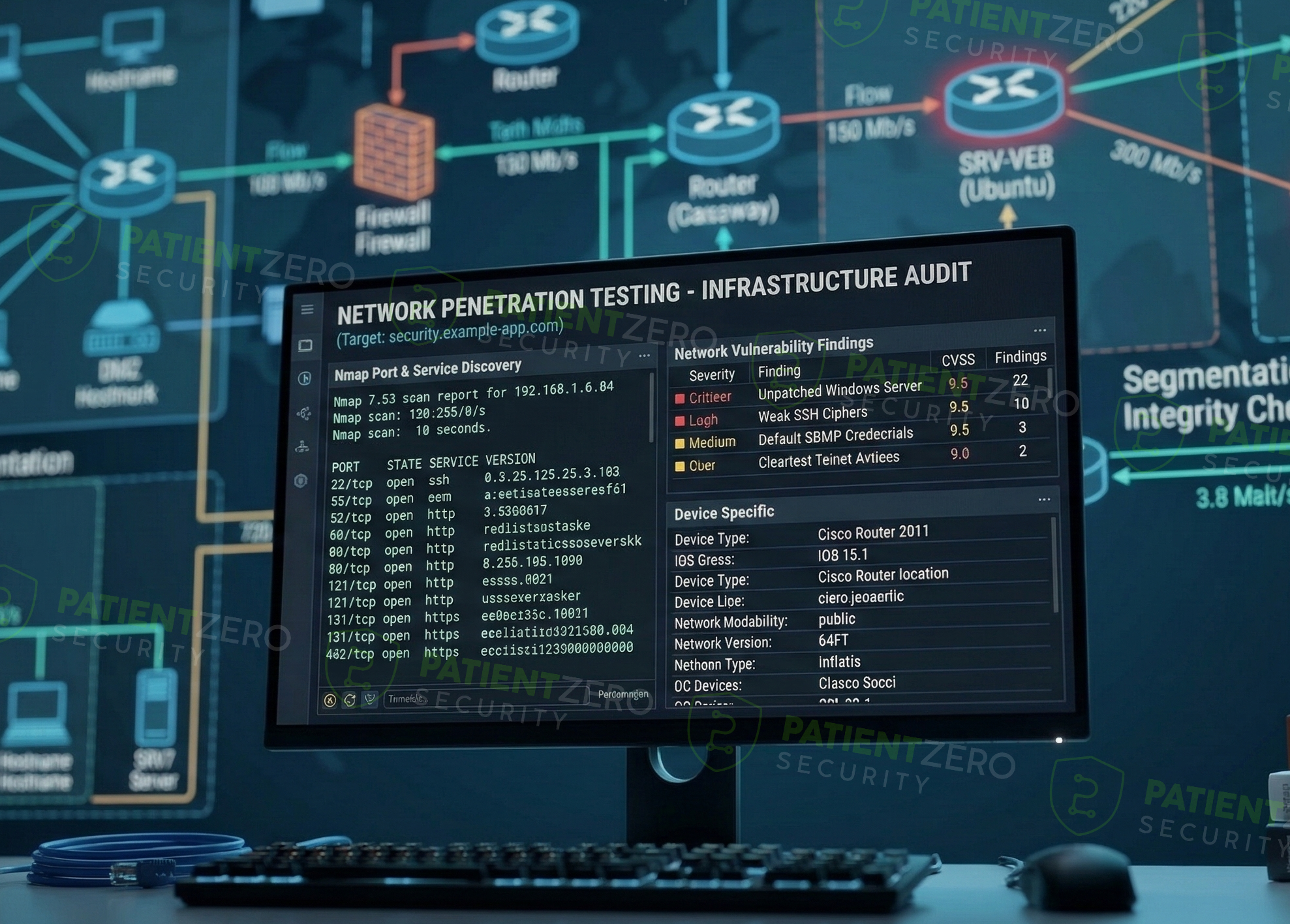
Network Penetration Testing evaluates the security of an organization’s network by identifying exposed systems, open ports, and running services that could be exploited.
What Network Penetration Testing covers
External attack surface analysis and internal lateral movement validation.
Network Penetration Testing evaluates the security of an organization’s network by identifying exposed systems, open ports, and running services that could be exploited by an attacker. The objective is to identify vulnerabilities and misconfigurations in network-accessible services and determine whether they can be leveraged to gain unauthorized access. Testing is conducted in alignment with PTES and NIST SP 800-115.
External Network Penetration Testing focuses on internet-facing assets by enumerating hosts, open ports, and exposed services, and assessing them for known vulnerabilities, weak authentication mechanisms, outdated software, and insecure configurations. Discovery and validation commonly use tools such as Nmap, Masscan, Nuclei, along with manual exploitation techniques where applicable.
Internal Network Penetration Testing assumes access to a system within the internal network, such as a workstation or VPN-connected host. From this position, internal IP ranges and subnets are scanned using tools such as Nmap or RustScan to identify vulnerable services and systems. Testing includes service enumeration, credential abuse, and Active Directory enumeration using tools such as BloodHound, CrackMapExec, and Impacket, with manual verification of privilege escalation and lateral movement where applicable.
Our network penetration testing process
A systematic approach from reconnaissance to domain compromise.
What you take away
Actionable results for network administrators and security leadership.
Ready to harden your network?
Every engagement includes a formal report and optional live readout call.

