Testing what defenses fail to see
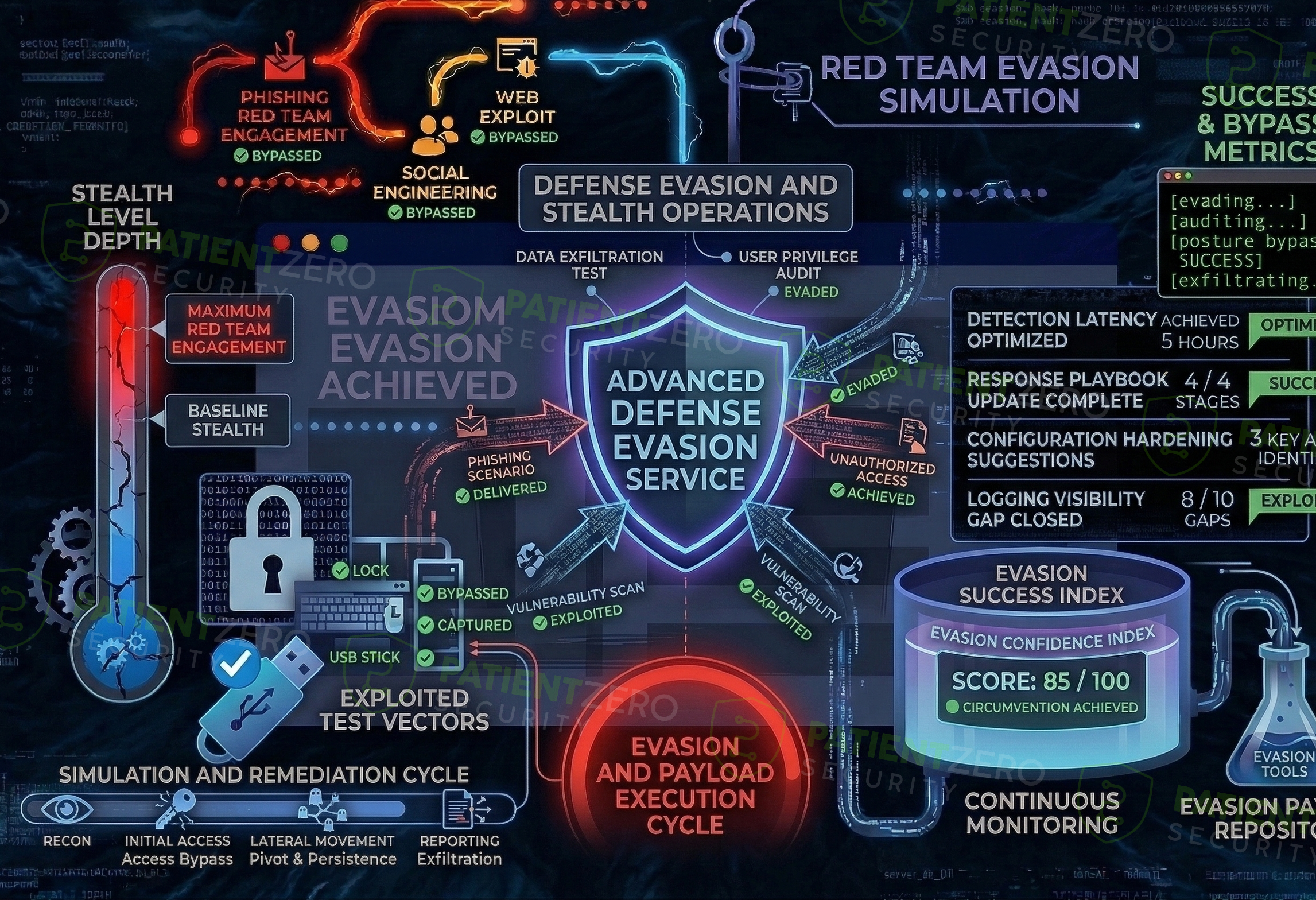
Defense Evasion Assessment validates how effectively your endpoint and detection controls identify and surface malicious execution techniques, using controlled custom payloads and realistic attacker tradecraft.
What Defense Evasion Assessment covers
Detection-focused assessments that validate how well your environment surfaces and responds to malicious execution techniques.
Defense Evasion Assessment evaluates the effectiveness of endpoint detection and response (EDR), behavioural monitoring, and supporting security telemetry by testing how reliably they detect malicious execution activity. The engagement focuses on detection capability, not long-term persistence or full compromise.
The assessment combines custom payload and tooling development with controlled execution of common attacker techniques to simulate realistic defence evasion in a safe and repeatable manner. Activity is carefully designed to reflect how adversaries commonly bypass controls while remaining within an agreed and tightly governed scope.
This service is ideal for organisations looking to validate EDR coverage, improve alert fidelity, and mature detection engineering by turning simulated attacker activity into concrete, actionable improvement opportunities.
How a defense evasion engagement runs
From defining detection objectives through to summarising coverage and improvement areas.
What you take away
Concrete insight into EDR effectiveness, detection gaps, and how to strengthen your monitoring coverage.
Ready to test your detection coverage against real techniques?
Schedule a consultation to define detection objectives, agree safe execution constraints, and plan a defense evasion assessment tailored to your tooling and environment.

