Security through configuration
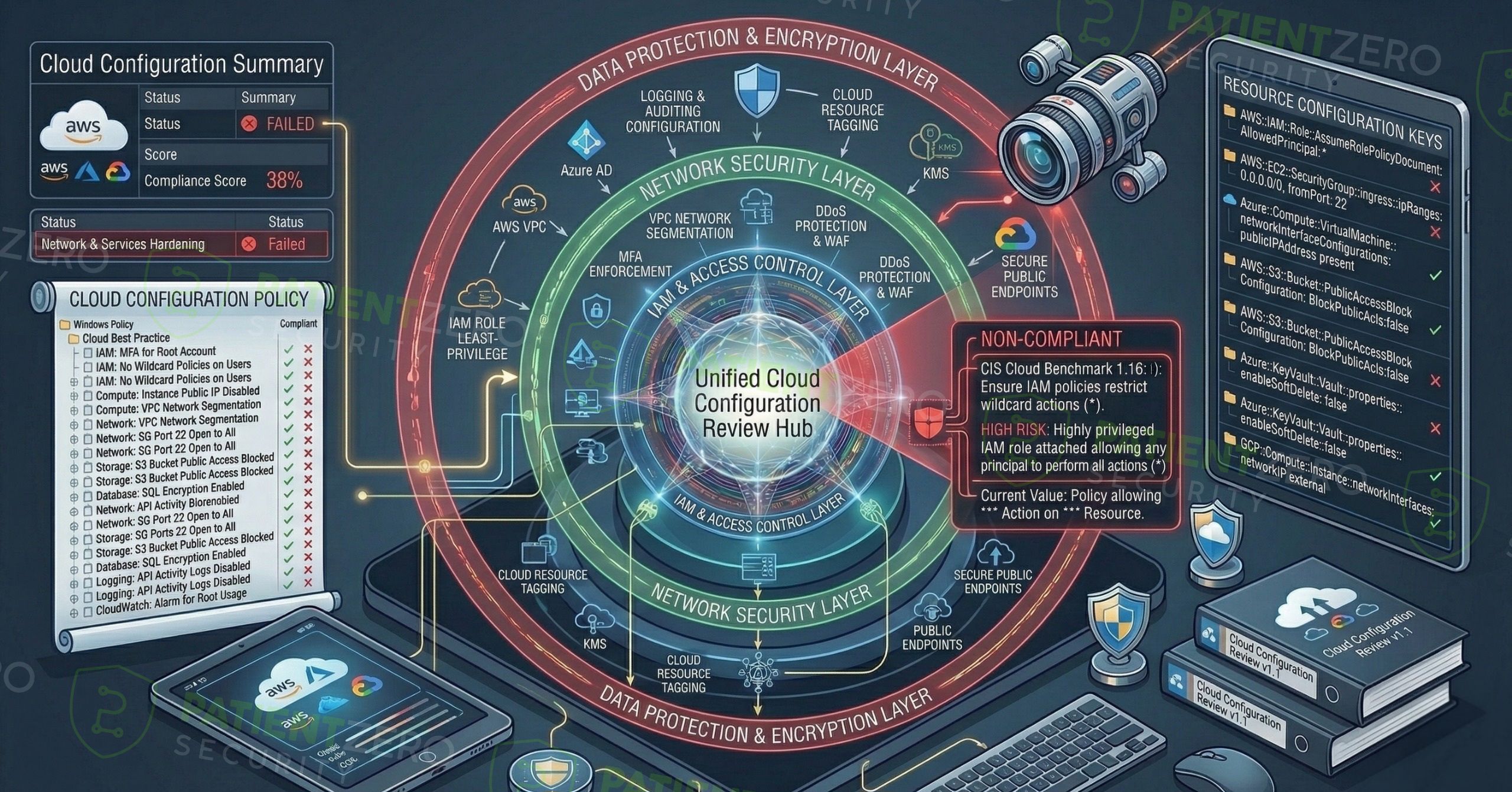
Cloud Configuration Review evaluates AWS, Azure, and GCP environments to uncover misconfigurations, excessive permissions, and insecure architectural patterns before they lead to data exposure or compromise.
What Cloud Configuration Review covers
Strengthen cloud security posture across AWS, Azure, and GCP without disruptive testing.
Cloud Configuration Review evaluates cloud environments to identify misconfigurations, excessive permissions, and insecure architectural patterns that could lead to unauthorized access, data exposure, or privilege escalation. The assessment focuses on configuration and identity security, rather than active exploitation, helping organizations strengthen their overall cloud security posture.
The review covers core cloud security controls including identity and access management (IAM), network exposure, logging and monitoring, storage permissions, and service-level configurations. Assessments are typically performed using a low-privileged or read-only account, reflecting a realistic access level while ensuring safe and non-intrusive analysis.
The service is aligned with CIS Cloud Benchmarks and relevant cloud provider security best practices, ensuring consistent and defensible coverage across AWS, Azure, and GCP environments. Automated posture analysis is combined with manual validation to reduce false positives and highlight misconfigurations that pose real risk, with particular attention to excessive privileges, publicly exposed resources, weak segmentation, and missing security controls.
Our cloud configuration review process
A focused review from discovering in-scope accounts to prioritized remediation guidance.
What you take away
Clear visibility into cloud misconfigurations and a practical plan to reduce risk across AWS, Azure, and GCP.
Ready to harden your cloud environments?
Schedule a consultation to walk through findings, prioritize remediation, and plan your AWS, Azure, and GCP security improvements.

