Security beyond compromise
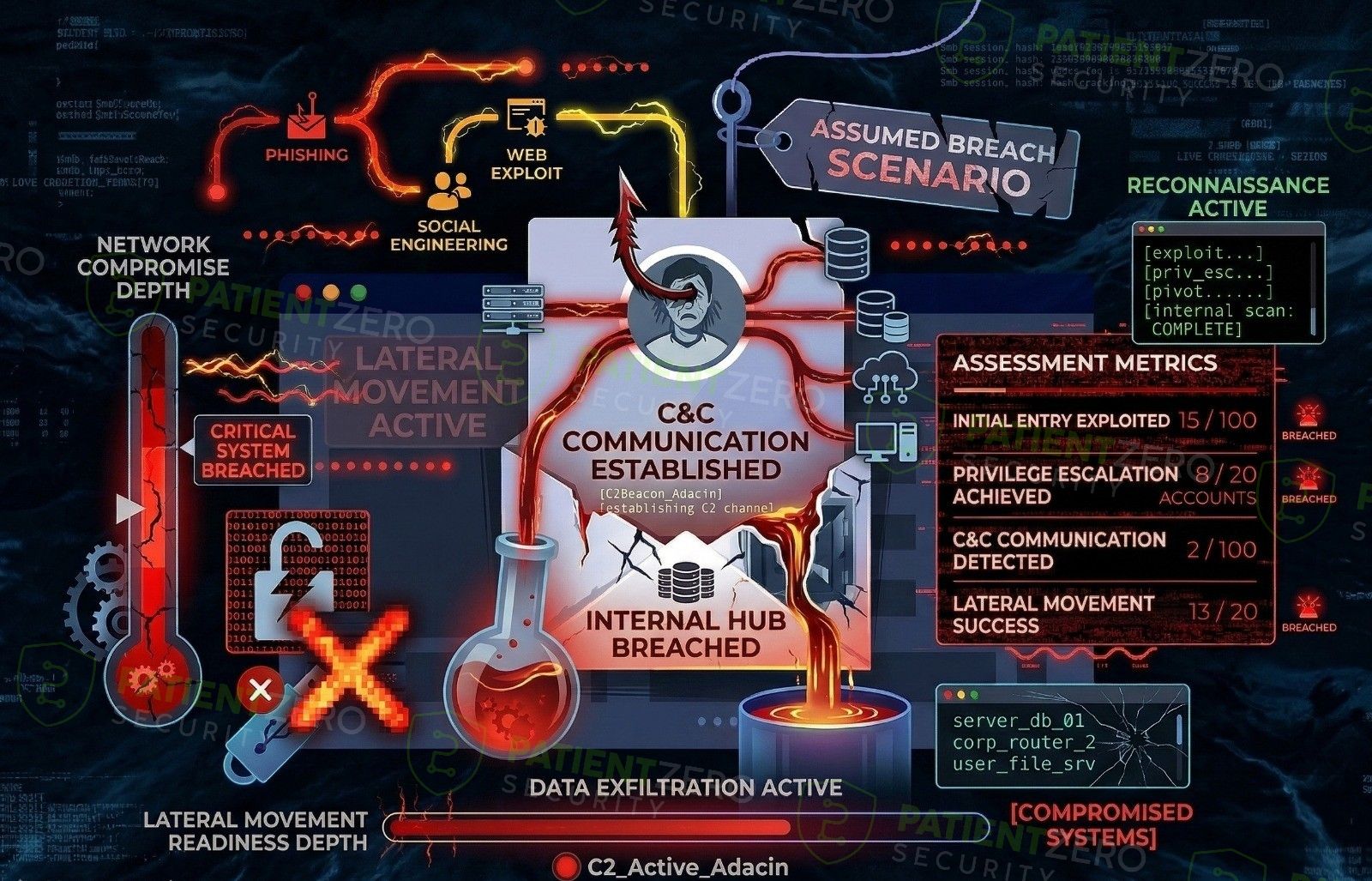
Assumed Breach Scenario evaluates your environment after compromise, starting from predefined internal access to understand how far an attacker can move, escalate, and impact the business.
What Assumed Breach Scenario covers
Post-compromise assessments that focus on internal movement, containment, and impact rather than perimeter defence.
Assumed Breach Scenario evaluates an organisation’s security posture after an initial compromise has already occurred. The engagement begins with predefined internal access, such as a standard user account or compromised workstation, and focuses on how effectively internal controls limit attacker movement, privilege escalation, and overall impact.
This service is particularly useful for assessing post-compromise security, including exposure to internal threats, compromised credentials, and insider-risk scenarios. Rather than testing perimeter defences, the assessment evaluates how well internal security controls, identity protections, segmentation, and monitoring prevent an attacker from expanding access within the environment.
The primary objective is to understand the blast radius of a single compromised user or system, and to determine whether attackers can escalate privileges, move laterally, or access high-value assets without being detected or contained.
How an assumed breach engagement runs
From starting conditions through to impact and blast radius analysis.
What you take away
Clear visibility into post-compromise risk, internal attack paths, and containment effectiveness.
Ready to validate your post-compromise resilience?
Schedule a consultation to define assumed access conditions, discuss scope, and plan an internal attack simulation tailored to your environment.

