Security tested under real attack
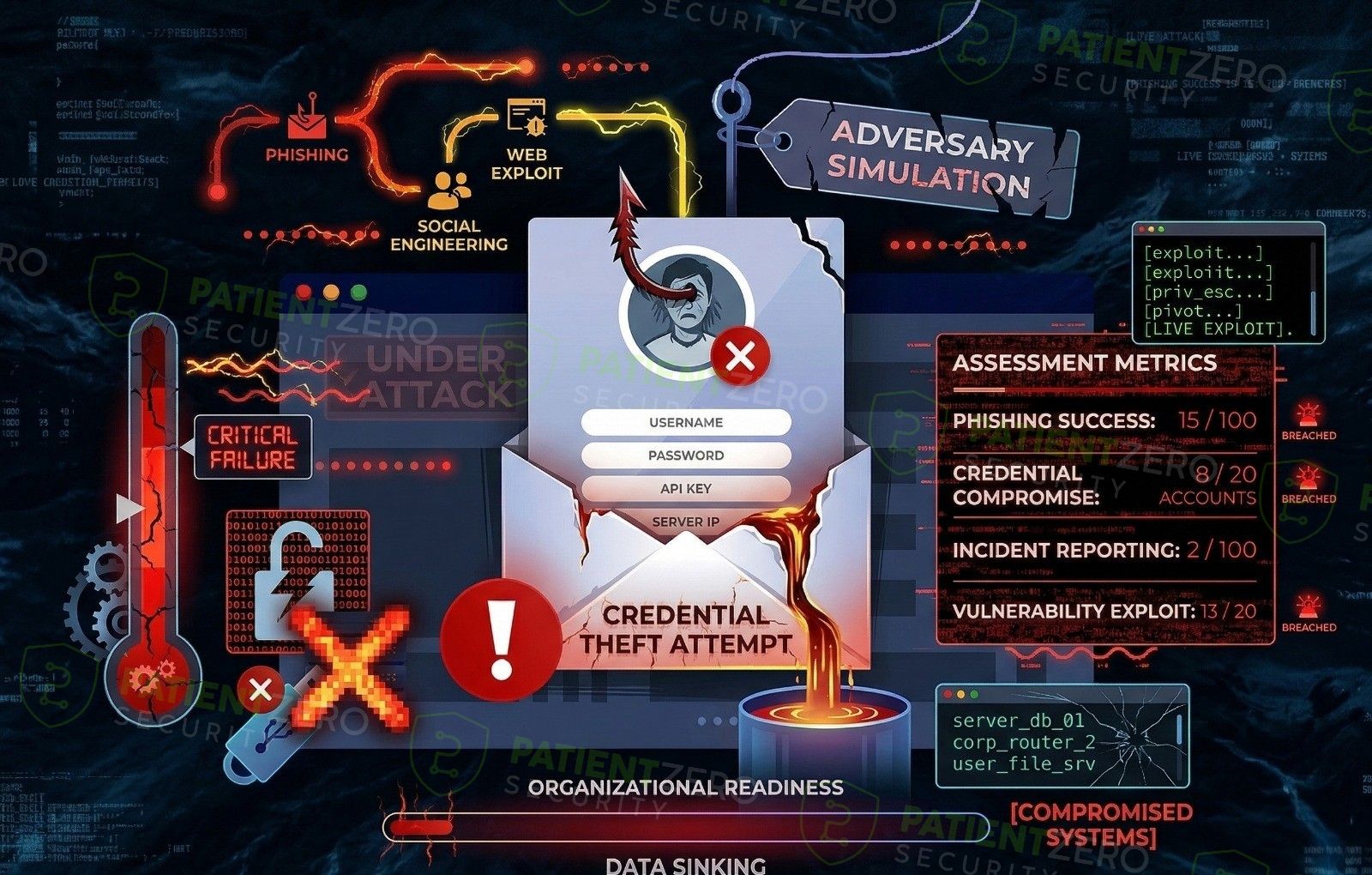
Adversary Simulation models realistic attacker behaviour using threat-informed tactics, techniques, and procedures to test how your organisation detects, responds to, and contains targeted attacks.
What Adversary Simulation covers
Threat-informed campaigns that evaluate how well your security programme performs under real attacker behaviour.
Adversary Simulation models realistic attacker behavior by simulating how attackers operate using known and commonly observed tactics, techniques, and procedures (TTPs). The engagement is threat-informed, meaning techniques are selected based on real-world attack patterns, industry trends, and relevance to your environment, rather than being tied to a single named threat actor.
The simulation follows the attacker's progression across the kill chain, including reconnaissance, initial access, execution, privilege escalation, lateral movement, and objective-driven activity. All simulated actions are mapped to the MITRE ATT&CK framework, giving clear visibility into which techniques are exercised and how effectively they are detected and responded to by existing controls.
The primary goal is to evaluate security effectiveness across people, process, and technology by observing how users, responders, and tooling perform during realistic attack scenarios, and where detection, response, and escalation processes break down.
How an adversary simulation engagement runs
From threat-informed planning through to post-engagement lessons learned.
What you take away
Insight into how real attackers would operate and how your defences actually perform.
Ready to run an adversary simulation in your environment?
Schedule a consultation to define objectives, agree rules of engagement, and plan a threat-informed simulation tailored to your organisation.

